Protect Disk is an effective data protection method on local disk, which has three protection levels - elementary, intermediate and advanced protection, and you can choose one according to your needs. Besides, it supports "Disable USB storage devices"and"Set USB storage devices as read-only".
The usage as follows:
1. Start Best Folder Encryptor, click the "Protect Disk" button.
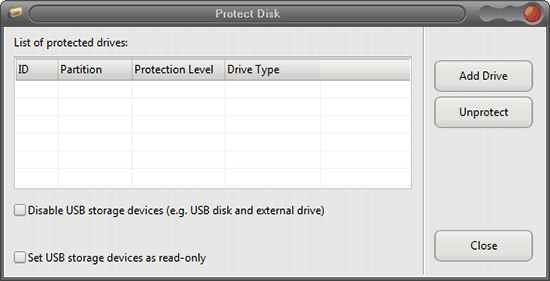
2. Click the "Add Drive" button in the pop-up window.
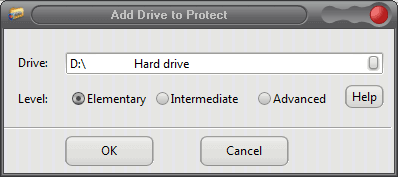
3. Select the drive you want to protect, and choose a protection level, then click OK.
The difference between the three levels of protection:
Elementary protection: The protected disk cannot be seen in My Computer or Windows Explorer, but you can access to it with command line (cmd mode).
Intermediate protection: The protected disk cannot be seen in My Computer, Windows Explorer or command line; but it can be accessed after reinstalling system or replacing the computer. Usually we recommend you use the intermediate protection.
Advanced protection: The protected disk cannot be accessed in any environment, even reinstall system or replace computer. Advanced protection enjoy the highest disk protection level which can completely hide disks on your computer. However, the protection will be in effect after you restart your computer.
It is easy to remove the disk protection. Select the disk protection record you want to remove and click the Unprotect button.
Disable USB storage devices and Set USB storage devices as read-only
Disable USB storage devices: When you do this, the USB storage device such as USB flash drive and external hard drive does not work when you connect the device to the computer. With this method you can protect your data stored on the computer from leakage.
Set USB storage devices as read-only: Files stored in the USB flash drives or external hard drives are able to be accessed but not modified, also you cannot wirte data into the devices.This kind of protection protects your data without influencing the normal use of USB devices.
Related reading:
How to remove the elementary disk protection without protection record?
How to remove the intermediate disk protection without protection record?
How to remove the advanced disk protection without protection record?