Best Folder Encryptor Tutorials
Best Folder Encryptor Introduction
Best Folder Encryptor is a professional and easy to use file and folder encryption software. It features superfast with high security. The encrypted files and folders are prevented from copy, deletion and movement. The function Temporary Unprotect automatically re-encrypts your file and folder when you're finished using so you don't have to worry about your file being left unsecured.
With Best Folder Encryptor you can also shred data, completely hide local hard disk, disable USB storage devices or set them as read-only.
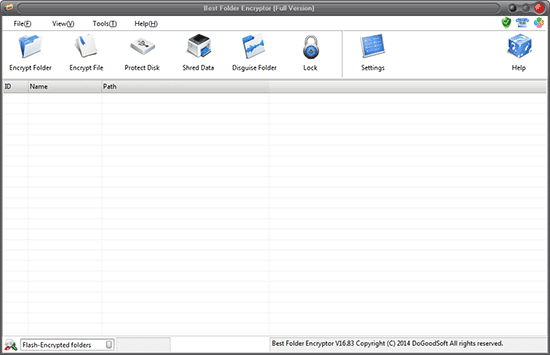
Figure 1
Basic Information of Best Folder Encryptor
Software Name: Best Folder Encryptor
Latest Version: 16.85
Last Updated: 07/04/2016
Size: 4.86MB
OS: WinXP/Vista/Win7/Win8/Win10
Category: File encryption, Folder encryption
Overview page: http://www.jiamisoft.com/best-folder-encryptor/index.html
Download page: http://www.dogoodsoft.com/best-folder-encryptor/free-download.html
Downlod and Install Best Folder Encryptor
Download
You can download Best Folder Encryptor by clicking "Free Download" at the download page.
Install
Double click the downloaded Best Folder Encryptor setup program(fsesetup.exe), and follow the step-by-step setup wizard to finish the installation. You can choose the installation directory to your personal preference.
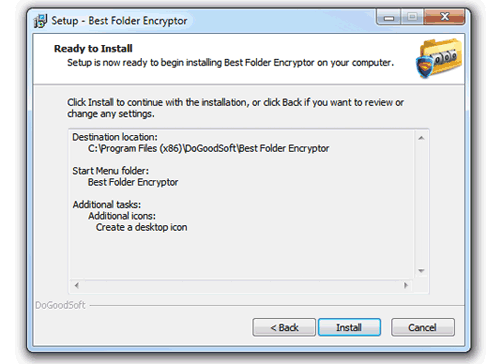
Figure 2
Then you can encrypt the files and folders using Best Folder Encryptor.
Folder Encryption and Decryption
Open windows explorer(Windows key + E), right-click the folder you want to encrypt and choose “Encrypt” in the pull-down menu. (see the Figure 3)
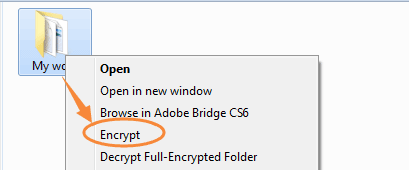
Figure 3
Enter your password and select the encryption type, then click Encrypt.
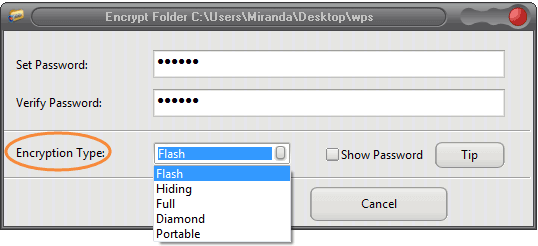
Figure 4
There are five encryption types in Best Folder Encryptor: Flash Encryption, Hiding Encryption, Full Encryption, Diamond Encryption and Portable Encryption.
Flash Encryption and Hidden Encryption boast of speedy encryption and decryption. The encrypted folder has no size limit, so these two methods are very suitable for encrypting large folders.
The flash-encrypted folder looks like the Figure 5.
Figure 5
As you can see from the picture above, a flash-encrypted folder becomes a shortcut and is 1 KB in size. It is not the real folder but you can reach the initial folder through this shortcut. Besides, please first decrypt the folder if you want to backup or move it, otherwise you just backup/move a shortcut of the folder.
If you choose Hiding Encryption, the target encrypted folder will disappear instantly, and you can only open/decrypt it in Best Folder Encryptor. Select "Hiding-encrypted folders" at the lower left corner in the main window of Best Folder Encryptor, and the hiding encryption record will appear in the list.
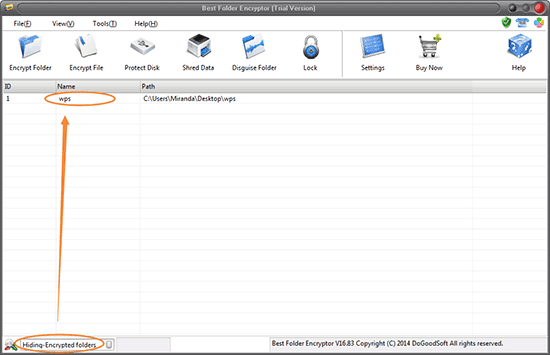
Figure 6
Click the encryption record and a password box pops up, enter the password and press "Open" or "Decrypt".
Full Encryption, Diamond Encryption and Portable Encryption feature strong encryption intensity and the encrypted folder can only be decrypted with the correct password. Yet these three encryption methods are a little slower compared to the first two methods, therefore they are perfect for important folders within 990M. Choose one of the three encryption methods, a window showing the encryption process will appear (see the Figure 7), and it will disappear automatically when the the encryption is completed.
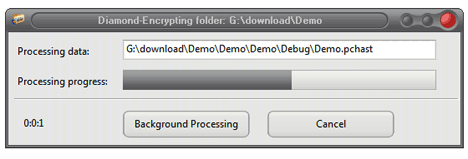
Figure 7
The window will be closed automatically after the process is finished.
Full Encryption encrypts all files in a folder in one time. To open the encrypted folder doesn't need the password but the files inside do. Right click the encrypted folder, select "Decrypt Full-Encrypted folder" and the folder is completed decrypted. (see the Figure 8)
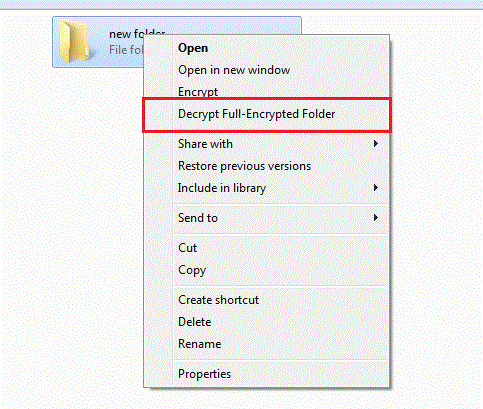
Figure 8
Diamond Encryption packs and encrypts a folder into an encrypted file with internationally mature encryption algorithm. The encrypted folder can only be accessible with a correct password. If you want to decrypt a Diamond-encrypted folder, double-click the folder, enter password in the pop-up box, and click "Decrypt".
Portable Encryption packs and encrypts a folder into an executable (.exe) file with internationally mature encryption algorithm. You can encrypt important data with this method, and it can be used on a computer where Best Folder Encryptor is not installed.
It must be troublesome to "enter password, decrypt and re-encrypt" every time when you use the encrypted folder.
Here we will show you the convenient "Open" feature of Best Folder Encryptor.
Open windows explorer(Windows key + E), double-click an encrypted folder, enter the correct password in the pop-up window and press "Open" (see the Figure 9).
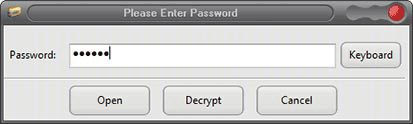
Figure 9
If it is a flash-encrypted folder, a "Folder Browser" appears when the folder is decrypted. Here, all the contents of the encrypted folder can be seen in "Folder Browser". (see the Figure 10)
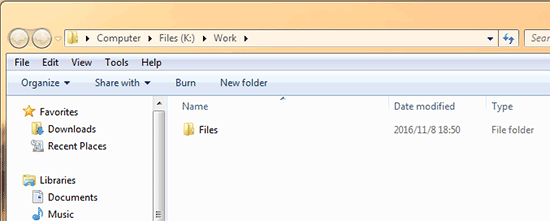
Figure 10
You can copy, move, delete, rename the files and folders inside Folder Browser just like you do in Computer/My Computer.
You can also copy/move the data in Folder Browser to Computer/My Computer, and vice versa.
After using files/folders in the encrypted folder, just close Folder Browser and there is no need to re-encrypt the folder.
Folder Browser is also used in Hiding Encryption, Diamond Encryption and Folder Disguise.
You can decrypt the encrypted folder temporarily by pressing the "Temporary Unprotect" icon at the top of the Control Board, meanwhile a small control window appears as the Figure 11 shows.
![]()
Figure 11
File Encryption and Decryption
In fact, the way of file encryption and decryption is the same as that of a folder. Open windows explorer(Windows key + E), right-click the file you want to encrypt and choose “Encrypt” in the pull-down menu. Then set your password and select the encryption type, and then click Encrypt. (please refer to the Figure 12)
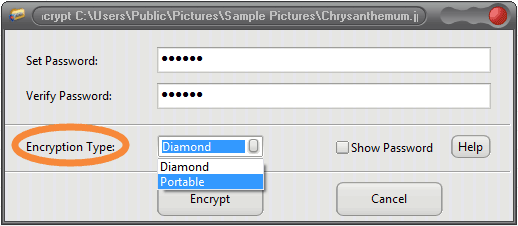
Figure 12
Figure 13 shows an encrypted file.
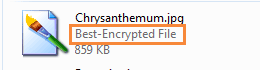
Figure 13
The file type becomes to "Best-Encrypted File". When you want to open an encrypted file, double-click the encrypted file, enter the correct password in the pop-up box, then press "Open". (see the Figure 14)
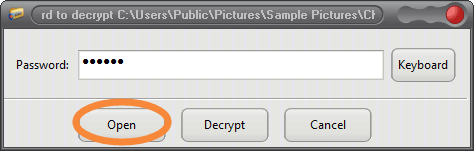
Figure 14
Interestingly, the file will be restored to encrypted status automatically after use and you don't need to re-encrypt it. If you click Decrypt, then the encrypted file is decrypted permanently. If you use "Portable Encryption", an exe. file is created at the place where the encrypted file locates.

Figure 15
Now we can delete the original file. To open a Portable-encrypted file, double-click the encrypted file and enter the password in pop-usp dialog box.
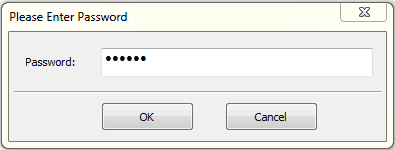
Figure 16
Then click "OK" and choose a route to place the opened file. After use, we can delete the temporarily-stored file.
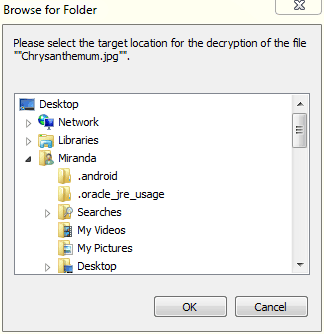
Figure 17
If you want to decrypt an encrypted file, save a copy of the file when it is opened and delete the encrypted one.
Disk Protection
It provides three levels of protection for a disk on your computer, that is, elementary, intermediate and advanced protection.
Start Best Folder Encryptor, click the "Protect Disk" button. Click the "Add Drive" button in the pop-up window. Select the drive you want to protect, and choose a protection level, then click OK. Now you cannot see the protected disk in Computer/My Computer.
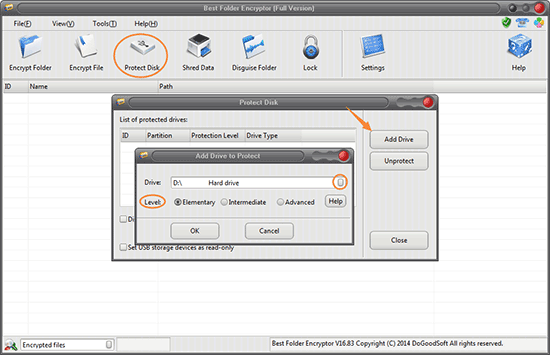
Figure 18
Three levels of disk protection:
Elementary protection: The protected disk cannot be seen in My Computer or Windows Explorer, but you can access to it with command line (cmd mode).
Intermediate protection: The protected disk cannot be seen in My Computer, Windows Explorer or command line; but it can be accessed after reinstalling system or replacing the computer. Usually we recommend you use the intermediate protection.
Advanced protection: The protected disk cannot be accessed in any environment, even reinstall system or replace computer. Advanced protection enjoy the highest disk protection level which can completely hide disks on your computer. However, the protection will be in effect after you restart your computer.
Besides, Best Folder Encryptor supports "Disable USB storage devices" and "Set USB storage devices as read-only".
You can set an Admin password for Best Folder Encryptor to prevent others from using this software without your permission.
Enhancements
Other enhancements include Disguise Folder, Shred Data, Lock, System Optimization Settings, System Garbage Cleanup, Disable USB storage devices or set them as read-only. Folder Disguise can disguise the target folder into a system folder so as to protect the data inside in a hidden and subtle way. (see the Figure 19)
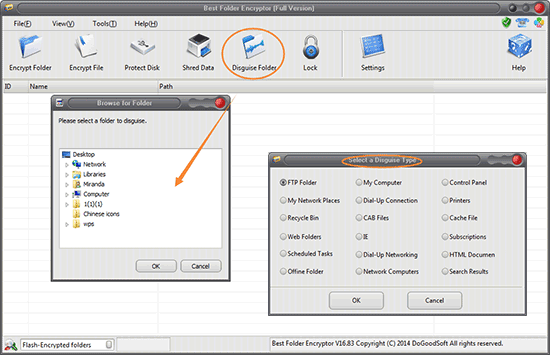
Figure 19