After Google’s decision not to provide end-to-end encryption by default in its new chat app, Allo, raised questions about the balance of security and effective artificial intelligence, one of the company’s top security engineers said he’d push for end-to-end encryption to become the default in future versions of Allo.
Allo debuted with an option to turn on end-to-end encryption, dubbed “incognito mode.” Google obviously takes security seriously, but had to compromise on strong encryption in Allo in order for its AI to work. (Allo messages are encrypted in transit and at rest.)
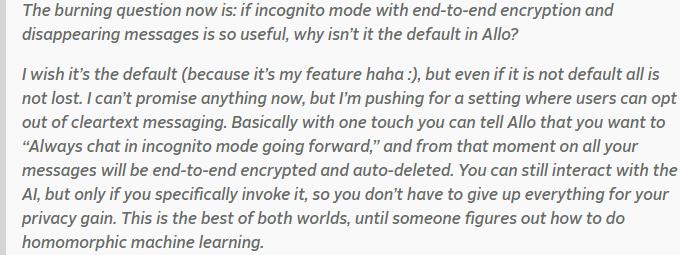
Thai Duong, an engineer who co-leads Google’s product security team, wrote in a blog post today that he’d push for end-to-end encryption in Allo — then quietly deleted two key paragraphs from his post. In the version he originally published, Duong wrote:
These two paragraphs have been erased from the version of Duong’s post that is currently live.
This edit probably doesn’t mean that Duong won’t continue to lobby internally for end-to-end encryption — his job is to make Google’s products as secure as possible. But Google, like most major companies, is pretty cagey about revealing its plans for future products and likely didn’t want Duong to reveal on his personal blog what’s next for Allo.
Even without the paragraphs on end-to-end encryption, Duong’s post offers interesting insight into Google’s thinking as it planned to launch Allo. For users who care about the security of their messaging apps, Duong highlights that it’s not encryption that matters most to Allo, but rather the disappearing message feature.
“Most people focus on end-to-end encryption, but I think the best privacy feature of Allo is disappearing messaging,” Duong wrote. “This is what users actually need when it comes to privacy. Snapchat is popular because they know exactly what users want.”
Duong also confirmed the likely reason Google didn’t choose to enable end-to-end encryption in Allo by default: doing so would interfere with some of the cool AI features Allo offers. For users who don’t choose to enable end-to-end encryption, Allo will run AI that offers suggestions, books dinner reservations and buys movie tickets. But the AI won’t work if it can’t scan a user’s messages, and it gets locked out if the user enables end-to-end encryption.
We reached out to Google to ask if the company asked Duong to edit to his blog post and will update if we hear back. Duong stressed that the post only reflected his personal beliefs, not those of Google — and we hope his advocacy for a default incognito mode comes to fruition.